In this post, we are introducing our early observations on a new version of the Satori botnet (Mirai variant). Data used for the analysis was extracted from the NASK darknet.
05.12.2017 03:57 UTC – 360 Netlab noticed a new uptick in the Satori activity. Some facts derived from the 360 Netlab post:
- Two ports are mainly targeted: 37215 (CVE-2015-7254 and 52869 (CVE-2014-8361).
- Attack activity started at 05.12.2017 around 04:00 UTC.
- At 05.12.2017 around 19:00 UTC, C2 sent kill scan command to the bots.
- These attacks are connected with previous attacks observed on port 23 and 2323.
We have decided to track TCP SYN packets on these ports in NASK darknet. First of all, we have analyzed daily amount of packets targeted into these ports. As stated in 360 Netlab posts, Satori related malicious activities had their beginning at 22.11.2017. According to this, we have monitored darknet traffic from 20.11.2017 to 06.12.2017.
Two different charts present activity in two different periods: from 20.11.2017 to 29.11.2017 and from 30.11.2017 to 6.12.2017. As our SISSDEN darknet analyzer is still during development phase, some time periods are missing. The amount of logged hours is shown next to the date. If the amount of hours is not specified, it means that the whole day was logged.
Before 22.11.2017, there were nearly no packets with destination port equal to 37215 and 52869. During the next days, amount of these packets increased, with a rapid burst of scans at 23.11.2017. However, these activities seems to be small in comparison to the sudden uptick at 5.12.2017 (where only 11 hours of traffic were captured).
In the beginning, we would like to focus on the days 5.12.2017 and 6.12.2017, as these are assumed to be the beginning of the Satori exploitation campaign. However, the earlier period of time (22.11-4.12) is still very interesting and valuable – treat it as a dessert.
5.12.2017 13:00 – 24:00 UTC
During this period of time, we have observed 483,548 unique IP addresses, where:
- At least one TCP SYN packet was sent on port 37215 or 52869,
- There were no other destination ports addressed than 37215, 52869, 23 or 2323.
Next chart presents top 10 localizations (by country) of these unique IP addresses. According to this, a significant amount of infections can be found in Egypt, Tunisia, Ecuador, Columbia and Argentina.
Now, let us have a look into the amount of packets sent from these IP addresses.
According to the presented data, not only 37215 and 52869 ports are targeted. There is also a significant amount of SYN packets destined for ports 23 and 2323. Attention, every SYN with destination port equal to 23 or 2323 had the same packet generation signature as a Mirai botnet:
IP DESTINATION = TCP SEQUENCE
It only confirms our suspicions that we are in fact observing the Satori botnet, which is a Mirai variant.
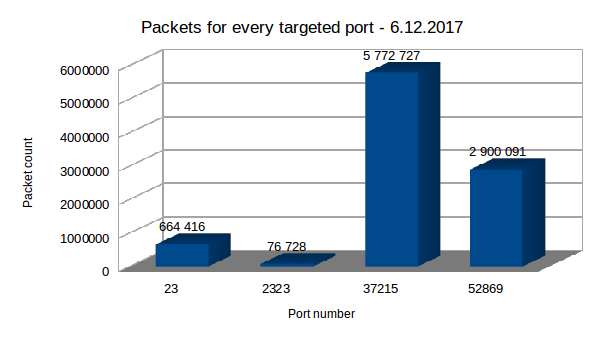
6.12.2017
The intensity of attacking/scanning activity significantly dropped. Most probably it is strictly connected with the sent C2 command mentioned in 360 Netlab post. However, it is still quite big and above the average. During this day, we have noticed 139,839 unique IP addresses, from which around 95,000 were noticed the previous day. Distribution of IP addresses over the world is very similar to the previous day.
However, we have observed a bigger amount of packets destined for port 23 and 2323. Similarly, every SYN packet targeting these ports had a Mirai-like signature:
IP DESTINATION = TCP SEQUENCE
To sum up, we have observed around 519,000 unique IP addresses which are believed to be the Satori botnet (according to the 360 Netlab information). Moreover, these IP addresses have the same packet generation signature during 23 and 2323 port scanning activities as Mirai.
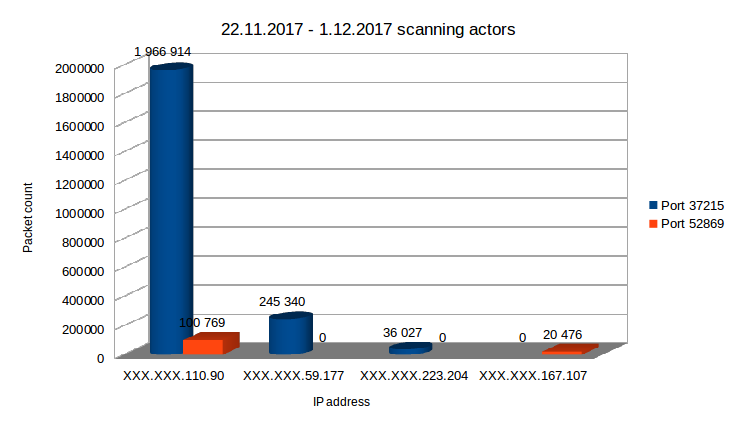
22.11.2017 - 01.12.2017
This period of time, predating the main event, is quite interesting. We have observed increased scanning activity especially on port 37215, although port 52869 was being scanned too. In comparison to the typical darknet traffic where the daily number of scans on these ports is of the order of hundreds, it seems highly suspicious. These scanning numbers are nowhere near the previously described activity of Satori botnet, although several important facts can be denoted:
- All of these scans were originating from only four different IP addresses: three of them are located in the USA and one is located in Italy.
- These four IP addresses were not observed in our darknet during the main Satori activity (05.12-06.12).
- These addresses did not scan any other port - only the two ports exploited by Satori.
The following chart presents the number of scans performed by each IP address. It is possible that these scans were related to the Satori exploitation campaign.
During the next few days, we are going to observe the fingerprinted IP addresses in the darknet traffic, so watch out for updates...