SISSDEN is a Horizon 2020 project aimed at improving the cybersecurity posture of EU entities and end users through the development of situational awareness and sharing of actionable information. It builds on the experience of The Shadowserver Foundation, a non-profit organization well known in the security community for its efforts in mitigation of botnet and malware propagation, free of charge victim notification services, and close collaboration with Law Enforcement Agencies, national CERTs, and network providers.
The core of SISSDEN is a new worldwide sensor network, which will be deployed and operated by the project consortium from within the EU. Passive threat data collection mechanisms will be complemented by behavioural analysis of malware and multiple external data sources. Actionable information produced by SISSDEN will be used for the purposes of no‐cost victim notification and remediation via organizations such as National CERTs, ISPs, hosting providers and Law Enforcement Agencies such as Europol’s European Cybercrime Center (EC3). SISSDEN will especially benefit SMEs and citizens, which do not have the capability to resist threats alone, allowing them to participate in this global effort, and profit from the improved information processing, analysis and exchange of security intelligence, to effectively prevent and counter security breaches. The main goal of the project is creation of multiple high-quality feeds of actionable security information that will be used for remediation purposes and for proactive tightening of computer defences.
This will be achieved through development and deployment of a distributed sensor network based on state-of-the art honeypot/darknet technologies and creation of a new EU based high-throughput data processing centre. SISSDEN will provide in-depth analytics on the collected data and develop metrics that will be used to establish the scale of most important security issues in the EU, and impact of the project itself. Finally, a curated reference data set will be created and published to provide a high-value resource for vetted academic and private industry security researchers.
Project objectives
The SISSDEN project has specified the following eight objectives as core goals of its operation:
- Create a large distributed sensor network. Over 100 passive sensors based on current and beyond state-of-the-art honeypot and darknet technologies will be deployed in multiple organizations, including all 28 EU member states and 6 candidate countries. These sensors will be used to observe malicious activities on an unprecedented scale, without intercepting any legitimate traffic.
- Advancements in attack detection. New types of honeypots, darknets and probes will be deployed to detect, analyse and alert on types of attacks not widely detected today, such as reflective DDoS amplification or attacks against Internet of Things (IoT) devices, which are expected to increase significantly in the coming years as a range of new network-centric technologies are embraced by consumers and SMEs globally.
- Advancements in malware analysis and botnet tracking. The large sensor network will be augmented by an innovative new generation of enhanced sandbox technologies designed for long running monitoring of malware specimen execution and behavioural clustering, to provide even more information on current threats.
- Improving the fight against botnets. Sensor and sandbox data collected will be used for detailed studies of botnet infrastructures. Long term observation of multiple families of current botnets will support anti-botnet research and law enforcement activities. Output will closely align with existing European anti-botnet and anti-cybercrime strategies, as well as providing support to proven strong LEA partnerships, such as with Europol EC3.
- Collect, store, analyse and reliably process Internet scale security data sets. The inherent challenges of building and continuously operating reliable data collection, storage, exchange, analysis and reporting systems at high volumes will be solved by multiple innovations in sensor and backend packaging, deployment, integration and data searching, based on consortium members’ extensive experience with “big data” approaches, high volume transactional and non-relational data systems.
- Share high-quality actionable information on a large scale. SISSDEN will produce large amounts of intelligence on current threats and all of it will be shared with stakeholders and the larger community, at no cost to them, for the purposes of remediation or for early warning. The project will distribute high-quality data feeds to the majority of the National CERTs in Europe, as well as worldwide, along with Law Enforcement Agencies, Internet providers, network owners and other vetted organisations fighting to defend their networks, SME customers, EU citizens and Internet Users against continuous attacks.
- Provide objective situational awareness through metrics. The consortium will have access to huge amounts of high-quality data on cyber threats: primarily obtained by the sensor network but also contributed by the members of the consortium. This unprecedented visibility will enable metrics developed as part of SISSDEN to offer a truly objective, non-vendor biased overview of the threat landscape in the EU and individual member states.
- Create and publish a large scale curated reference data set. A significant subset of the data produced by SISSDEN will be made available to vetted researchers and academia, addressing the clear and urgent need for large scale, high quality, recent security datasets in order to improve or test defensive solutions. This should become a valuable new resource for powering security research excellence in Europe.
Technical architecture
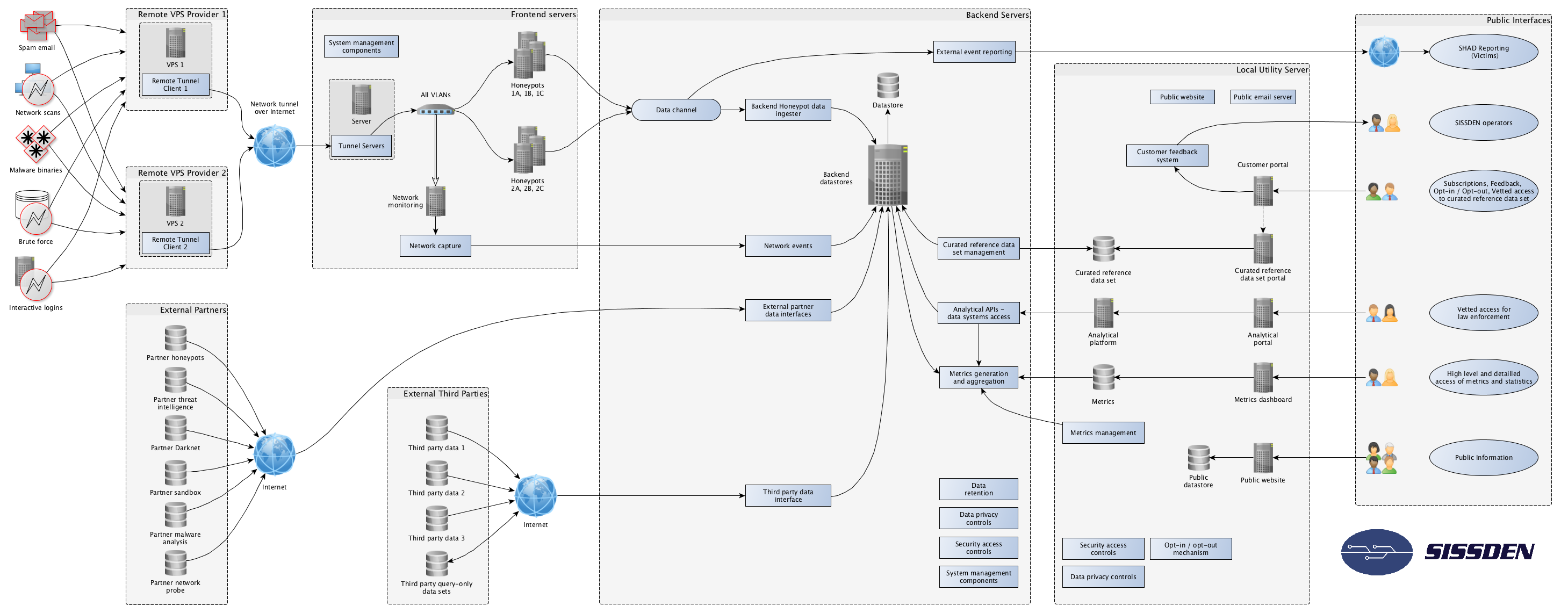
The figure below provides a simplified visualization of the SISSDEN initial technical architecture.
As part of the project, SISSDEN has procured a new EU datacentre and is deploying a sensor network of 100+ sensor end points throughout Europe and the wider world. Components located at the EU datacentre include the Frontend Servers, Backend Servers and Utility Server pictured on the diagram. The sensor network consists of remote VPS Provider end points located at various VPS hosting providers (i.e. outside the EU datacentre), configured as transparent network tunnel endpoints forwarding traffic to the EU datacentre. SISSDEN will collect attack data such as network scans, spam email, malware binaries, brute force attacks, interactive attacker logins etc.
Remote endpoint sensors (VPS)
Each remote endpoint sensor will contain only the minimum amount of configuration and management capabilities required to securely participate as one end of a transparent network tunnel. They will be configured to essentially act as a long virtual Ethernet cable between the VPS and SISSDEN’s local data centre frontend. At the Frontend in the EU Datacentre, a tunnel server will terminate each transparent layer 2 Ethernet tunnel and deliver the Ethernet frames to an isolated, dedicated Virtual Local Area Network (VLAN).
Frontend servers
Traffic from the remote sensor endpoints will be received by multiple types of honeypot systems, implemented as VMs, running on the EU Datacentre Frontend. Each honeypot VM will emulate one or more potential vulnerabilities and collect data about attacks observed against those vulnerabilities. The honeypots will have a standard configuration and standard data collection formats enabled. Their data collection capabilities will be complemented by network packet capture components running on separate VM instances that will listen to all traffic coming to them. SISSDEN system management components will be required to centrally manage all VM configuration, orchestration and operations.
Honeypot data and data from the network capture components will be ingested into the Backend datastores located at the Backend Servers at the EU Datacentre.
External partner and third-party systems
The data collected by the SISSDEN sensor network will be supplemented by data from external systems operated by SISSDEN partners. These will include separate honeypot networks, darknets, sandbox and malware analysis systems, threat intelligence platforms etc. As with the sensor network, data from these systems will be ingested in various forms and stored in the Backend datastores.
Additionally, previous work in the project by partners has identified various candidate external third party data sources that could potentially be included as sources of enrichment for SISSDEN’s own data collections.
To avoid unnecessary software development, SISSDEN will make use of and extend background partner systems, which will aggregate data from multiple sources and provide a well-defined RESTful API for accessing normalized datasets.
Backend Servers
Data from SISSDEN’s various data collection systems will be represented in multiple formats, such as live-streamed events, log files, PCAP files, and other file format data. Most of these data types will need to be stored in their raw format in local data storage systems, at least for predetermined periods/repository size quotas, and some of the data types will also require parsing, normalization and ingesting into backend data indexes in support of free daily remediation report generation, data analytics and ad-hoc queries.
At the Backend Servers and Utility Server, SISSDEN components will be required to deploy and manage the data ingest and storage systems. This will include managing security access controls, data retention, data privacy controls etc.
External reporting system
One of the main purposes of the SISSDEN project is to collect Internet scale, timely security event data and make it available at no cost to vetted National CERTs, Network Owners and organizations who sign up for SISSDEN’s free daily alerts.
The various sources of data collected by SISSDEN, such as honeypot and darknet data, malware analysis data, and botnet tracking information – as well as ingested external third party data sources – will be collected and stored locally in the SISSDEN backend. Each day recipients who have voluntarily signed up for free reporting will receive by email multiple reports, covering different types of potentially malicious activity detected by SISSDEN on their nominated, verified IP / ASN / CIDR addresses.
To avoid unnecessary software development, reduce costs and provide access to a large, proven, vetted reports consumer base, SISSDEN will make use of and extend Shadowserver’s existing background daily reporting system. SISSDEN components will be required to process collected data and provide it to Shadowserver’s external reporting system for distribution.
Utility Server
Various analytics will be performed on the data collected by SISSDEN. An analytics platform will be developed, and hosted on the Utility Server. These analytics solutions will provide additional insight into threats propagating in the Internet, pooling together partner resources dedicated to the project. In addition, metrics will be applied to the collected datasets to provide improved situational awareness. They will be used as a basis on which informed decisions can be made to mitigate threats. Curated reference datasets will also be made available to vetted researchers through the Utility Server. Interactions with the above are described in more details in this document and take place through the external interfaces illustrated in the diagram (with the exception of the analytics platform, which will only be available to SISSDEN partners).
SISSDEN will present a number of systems to interact with the public and external partners. These will include a Public website (mostly containing information about the project), email communication (reports), a Customer Portal, Metrics Dashboard etc. Hosted on the Utility Server, these public facing systems will include mechanisms to communicate with the consortium, sign up to request free of charge reports, gain access to the curated reference data set, provide customer feedback, and manage opt in/out and data privacy issues.