The primary objective of the SISSDEN project is to offer National CERTs, ISPs and network owners free reports on malicious activity detected on their networks. In SISSDEN, collection of this type of information is achieved primarily through honeypots. One of these honeypots is dedicated towards the detection of amplification DDoS attacks. This specific category of DDoS attacks utilizes UDP-based open, amplifiable services to reflect packets to a victim, by spoofing the source IP address of the packets sent to the amplifier to the victim's IP address. Depending on the protocol and type of open services abused, the size of the original packet content sent by the attacker can be amplified in the service response multiple times (even by a factor of hundreds), flooding the victim with packets and enabling DDoS. Honeypots that emulate open and amplifiable services can be used to detect this kind of abuse. However, as the source of these attacks is spoofed to the victim address, it is possible only to report on victims being abused not on the source of the DDoS.
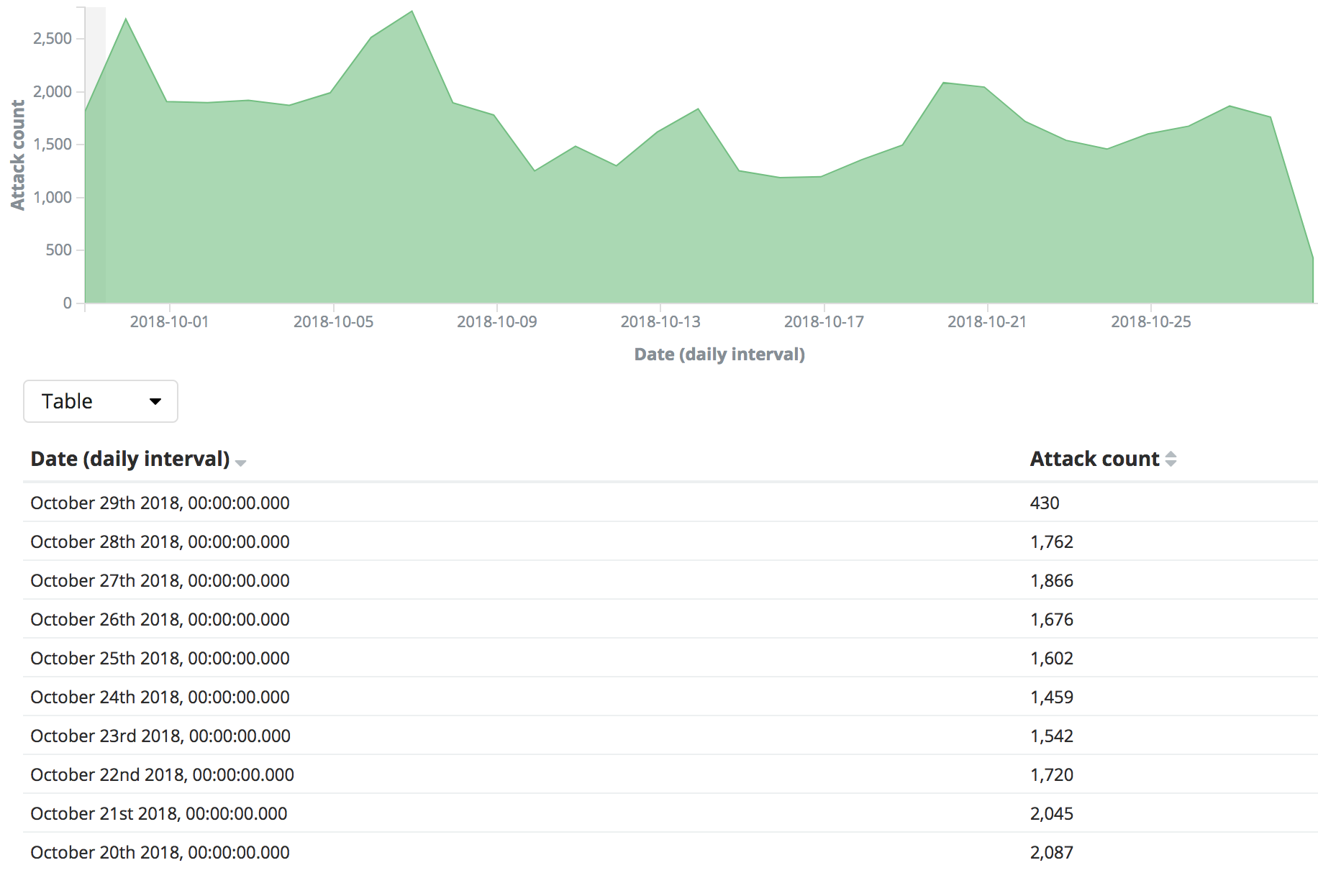
The chart below illustrates the scale of these types of amplificable DDoS attacks in Europe based on SISSDEN data. Looking back from 29th October over the last 30 days, over 53,000 attacks have been observed against over 36,000 victims with IP space in Europe, with open NTP (port 123/udp), DNS (port 53/udp) and chargen (port 19/udp).
You can read more about our DDoS attack observations in our blog entry on observations on DDoS attacks in 2018. For more insight into how amplifiable DDoS attacks work check out this writeup and paper by Christian Rossow.
The Amplification DDoS Victim report that is being sent out includes the IP that is being targeted (i.e. the victim), information about the type of service being abused for the DDoS, DDoS start times as well as end times if available, request used (if available). See the format of the report below.
| Field | Description |
| timestamp | Time that the amplification DDoS was registered in UTC+0 |
| ip | The IP address being DDoSed |
| protocol | Protocol used for the DDoS reflection attack |
| dst_port | Port being used for the DDoS reflection attack (ie. associated with the service/protocol used for amplification) |
| tag | Additional attack information for example, service name used for attack |
| src_port | Source port of the spoofed packets being sent |
| hostname | PTR record of the target IP |
| asn | ASN announcing the target IP |
| geo | Country where the target IP resides |
| region | State / Province / Administrative region where the target IP resides |
| city | ASN of where the target IP resides |
| naics | North American Industry Classification System Code of the target IP |
| sic | Standard Industrial Classification System Code of the target IP |
| request | Request being used to generate the amplification attack, if recorded |
| count | Count of requests sent as part of the amplification attack, if recorded |
| bytes | Bytes sent as part of the attack |
| sensor_geo | Geolocation of sensor that detected the reflected amplification attack |
| sector | Sector the target IP belongs to |
| end_time | The time when the attack ended (if recorded by the source) |
| public_source | Source of the data, for cases where the source accepts being credited |
As of 25th October 2018, the Amplification DDoS Victim report has been included in Shadowserver's reports and is being sent to 92+ National CSIRTs and 4200+ network owners (including 1200+ in the EU) as part of the free daily victim remediation feeds, in easily parsable CSV format. Anonymized samples of the reports being sent out are available here. If you are a network owner or CSIRT and wish to receive reports from SISSDEN you can either subscribe directly to Shadowserver's feeds or do so through the SISSDEN Customer Portal, which will be made available soon. Existing Shadowserver subscribers will receive the free Amplification DDoS Victim report automatically on a daily basis.
This is the fourth SISSDEN report that is being sent out to the CSIRT community (and to all subscribed network owners) after the ICS Scanner report (going out since the 20th September 2018), HTTP Scanner report (going out since 13th September 2018) and the Brute Force report which has been going out on a daily basis since April 2018.