General information
On 4 February 2018, 360Netlab informed the world about ADB.Miner – the Android botnet spreading in a worm style. ADB.Miner activity started on 3 February and it continues. On 6 February, 360Netlab provided another blog post with more details.
Some basic facts about the worm derived from the 360Netlab blog:
- It spreads in a worm-like manner over TCP port 5555 (ADB debugging interface on Android devices), which should be normally closed
- Infected devices are mainly located in Asia (China, Hong Kong and Korea)
- All generated income is connected with a single wallet:
44XT4KvmobTQfeWa6PCQF5RDosr2MLWm43AsaE3o5iNRXXTfDbYk2VPHTVedTQHZyfXNzMn8YYF2466d3FSDT7gJS8gdHAr - It uses Mirai's code for SYN scanning activity
- It does not have a C&C server
Some of the fragments were not highlighted by the accident. Mirai SYN scanning activity can be easily distinguished by the following PGA (Packet Generation Signature):
TCP SEQUENCE = IP DESTINATION
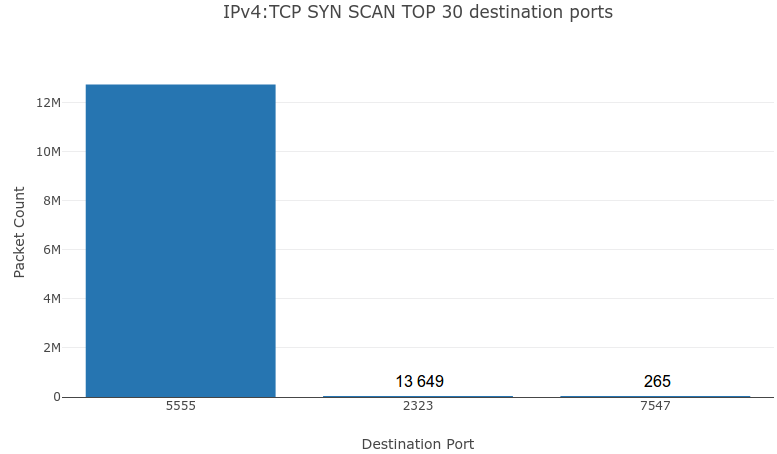
Such a signature included in the packet can be easily tracked in the darknet traffic. According to this, we have run a query for the TCP scans on port 5555 with the above mentioned PGA signature (from 04.02.2018 to 08.02.2018 07:00 AM UTC). As a result, we have obtained almost 13 million scanning packets and about 35 thousand unique IP addresses.
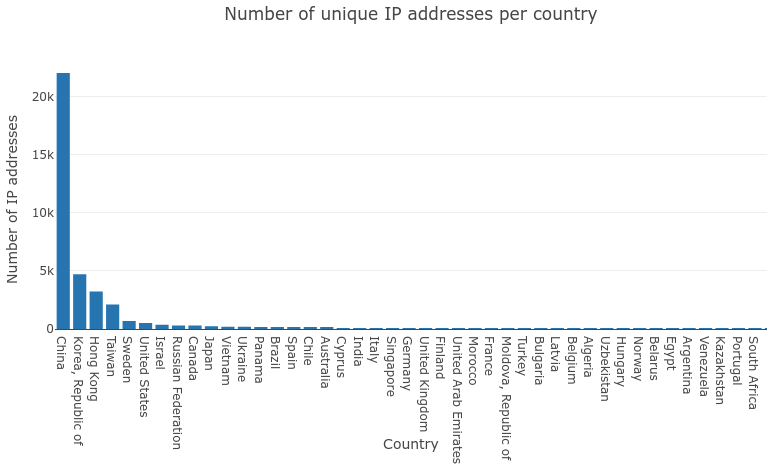
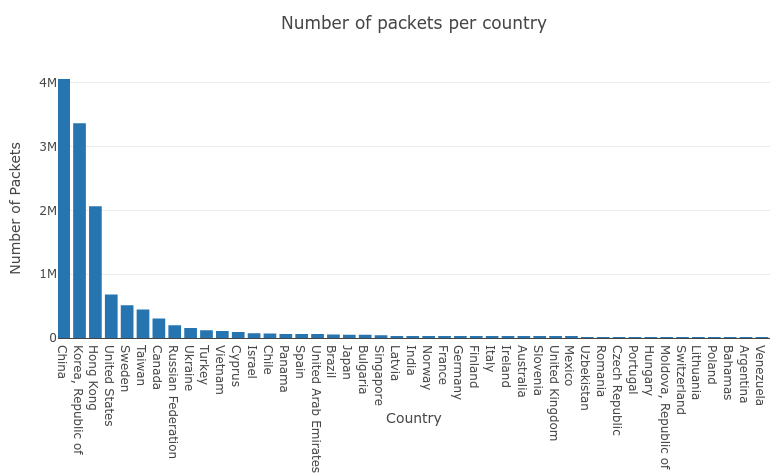
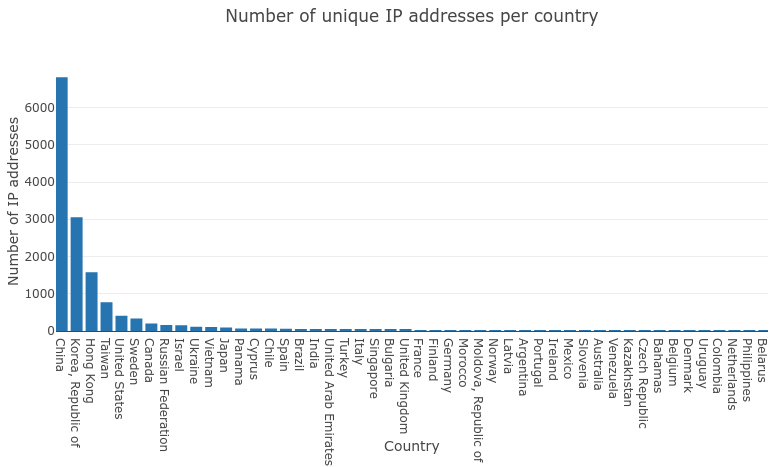
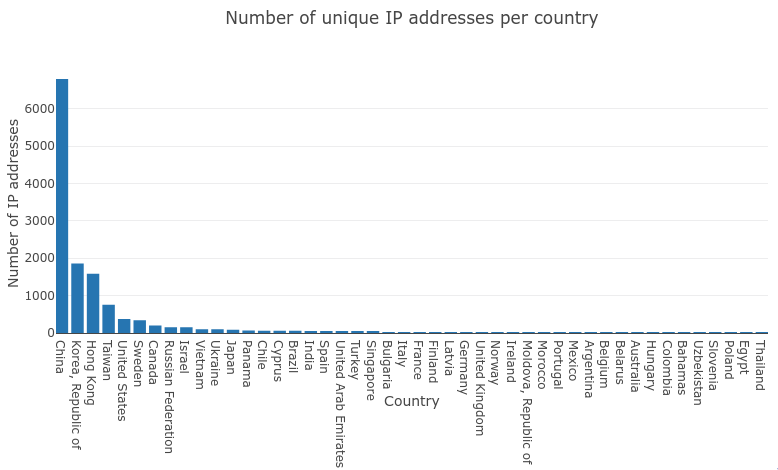
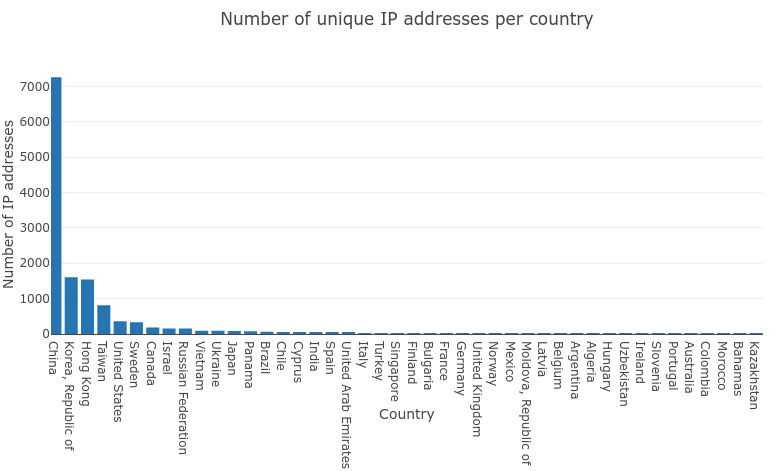
Firstly, let us have a look into the IP address distribution among countries. As it was mentioned before, we have observed about 35,000 unique IP addresses originating from the 90 different countries. The largest number of IP addresses was assigned to China (21,036). The following chart presents top countries in terms of the number of observed unique IP addresses. The next chart presents top countries in terms of the number of scans (packet numbers).
Interesting is the fact that these IPs occasionally scanned two different ports using the Mirai SYN scan signature (2323 and 7547), which are frequently scanned by Mirai and its variants:
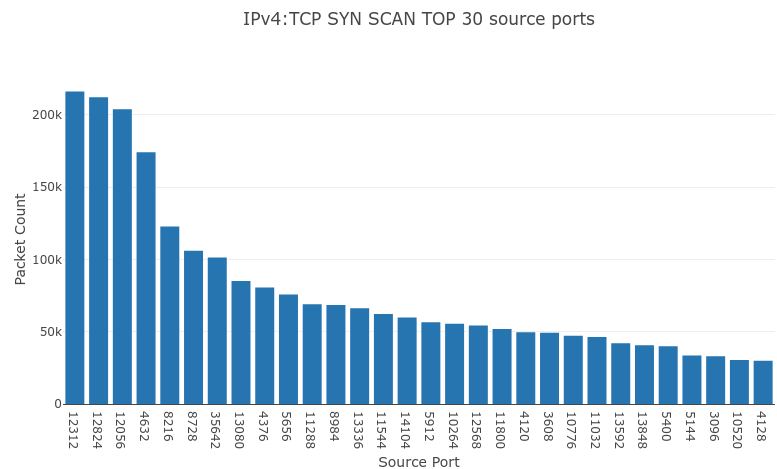
Let us take a look into source ports now. They do not seem completely random, because:
- About 10% of all scans had only 7 different source ports
- Port numbers seem pretty low for the source ports used for SYN packets
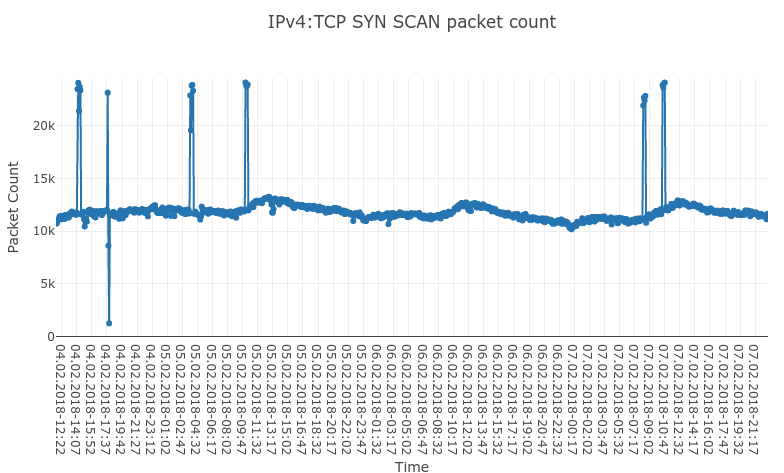
Finally, the following chart presents a timeline of the scanning activity (taken from the 84-hour long period). Typically, we are observing around 12,000 scans per 5 minutes. However, some occasional upticks can be observed. They usually last about 20 minutes and during this time the number of scans doubles.
Because of the NAT and DHCP, it is hard to point out the exact number of infections (we can only provide some estimations), thus we have decided to check the daily number of unique IP addresses:
05.02.2017 - 14 774 unique IP addresses
06.02.2017 - 13 413 unique IP addresses
07.02.2017 - 13 554 unique IP addresses
According to these numbers, we can assume that there are about 14,000 infected devices (not 35,000). We are planning to observe this worm activity and its spreading capabilities. However, as there is no C&C server, we are not predicting any new or unusual behaviors originating from this specific threat.