General information
Some time ago, we have written about Satori botnet fingerprinting. Right there, we have fingerprinted more than half a million infected machines. However, Satori's C2 was quickly sinkholed by the security community.
Not so long ago, 360Netlab informed the world about Satori.Coin.Robber variant, which is robbing ETH BitCoins by exploiting Claymore Miner software. This particular variant was performing scanning activities on ports 37215, 52869 and 3333.
It was also possible to notice some scans on port 81, because Satori was exploiting IP cameras.
On 10.02.2018, 360Netlab informed via twitter (here and here) about a new Satori variant, which is exploiting Dasan Routing devices via port 8080.
Let us look into some details concerning Satori.Dasan, which were provided by 360Netlab and Radware. First of all, it is trying to exploit CVE-2017-18046 and perform a remote command execution by a buffer overflow. Bots are looking for vulnerable Dasan devices with port 8080 opened. However, they are not performing any exploitation actions. This botnet has a central exploitation server, which is responsible for the infections (185.62.188.88). This IP address can be derived from the TXT record of f.rippr.me hostname.
Fingerprinting in darknet
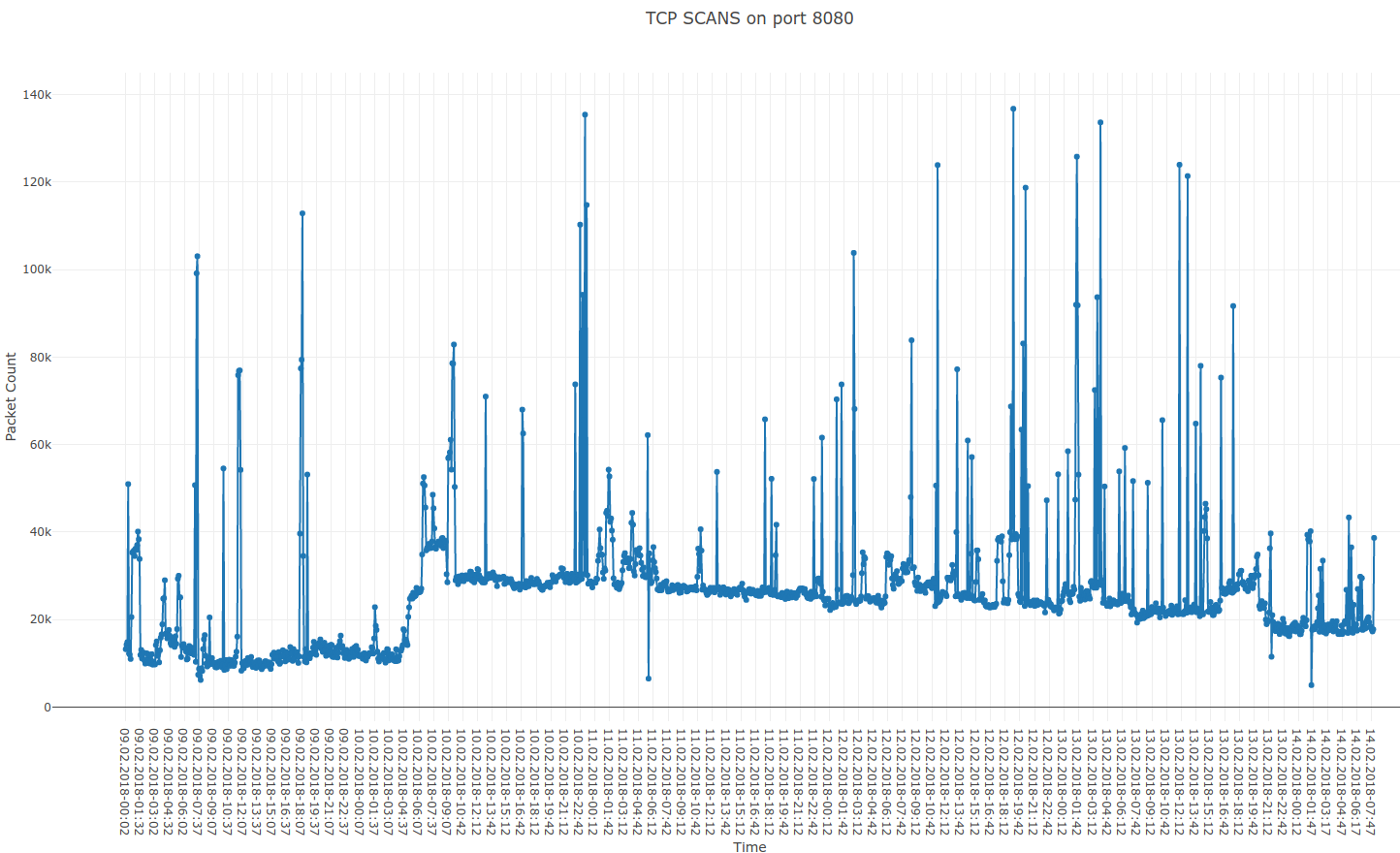
So, in the beginning we have checked the total number of scans observed in darknet on port 8080. The uptick around 10.02.2018 06:00 UTC was very clear, so we have decided to investigate further. A small but noticeable drop down can be noticed on 13.02.2018 20:00 UTC, but we will discuss it later.
Here is an interesting part. Variant described in the previous blog post was scanning ports 23 and 2323 with Mirai signature. However, for the more interesting scanning on port 37215 and 52869 we have found no signatures. This has changed - nowadays almost every port targeted by Satori is using Mirai signature (TCP SEQUENCE NUMBER = IP DESTINATION), whether it is port 3333, 8080, 37215 or 52869. Probably, this behavior can be connected with the centralized exploitation server. As bots are not responsible for the exploitation themselves, they are probably just using Mirai code for efficiency.
According to this, we were looking for the IP addresses that were scanning port 8080 (only this port) with a Mirai signature.
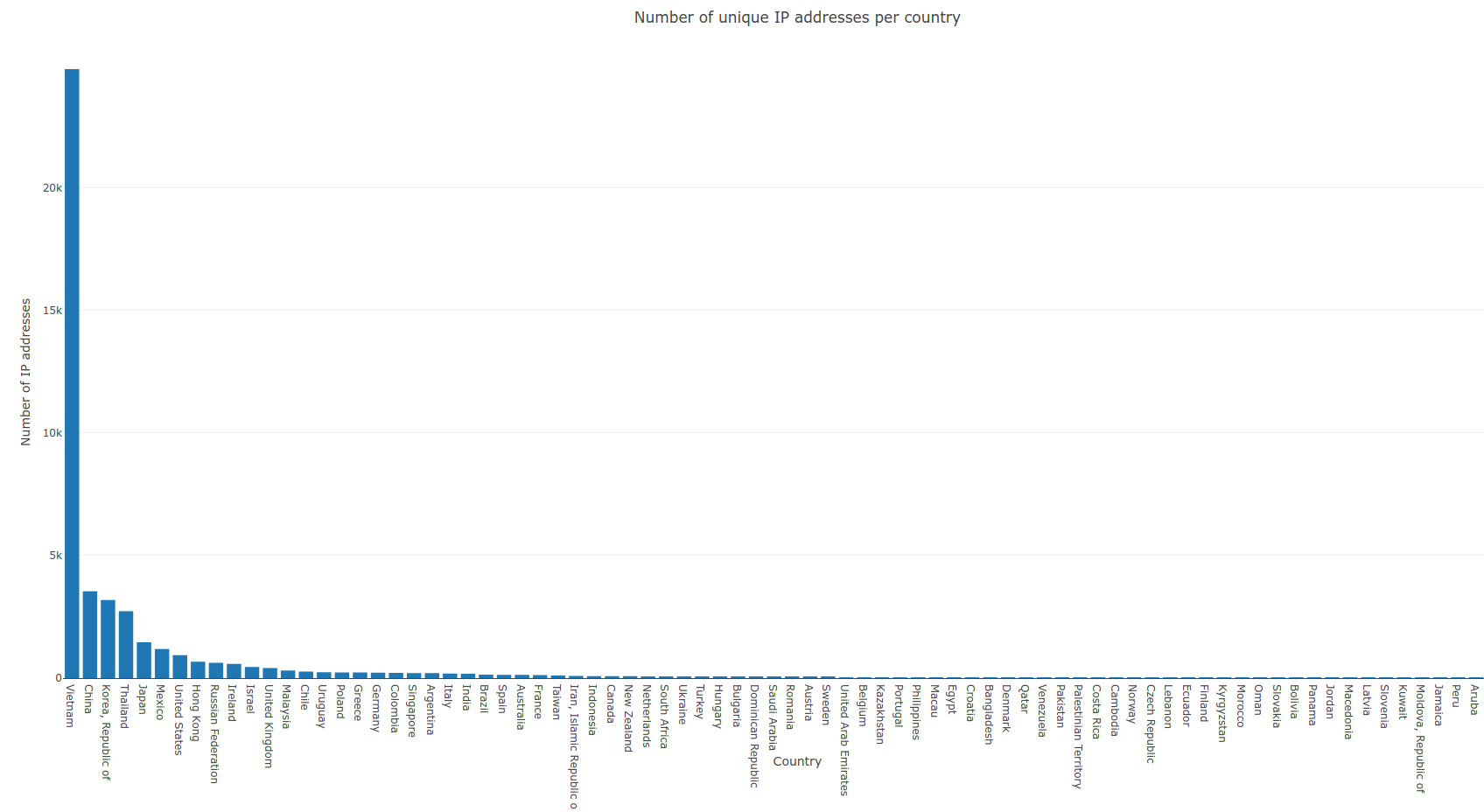
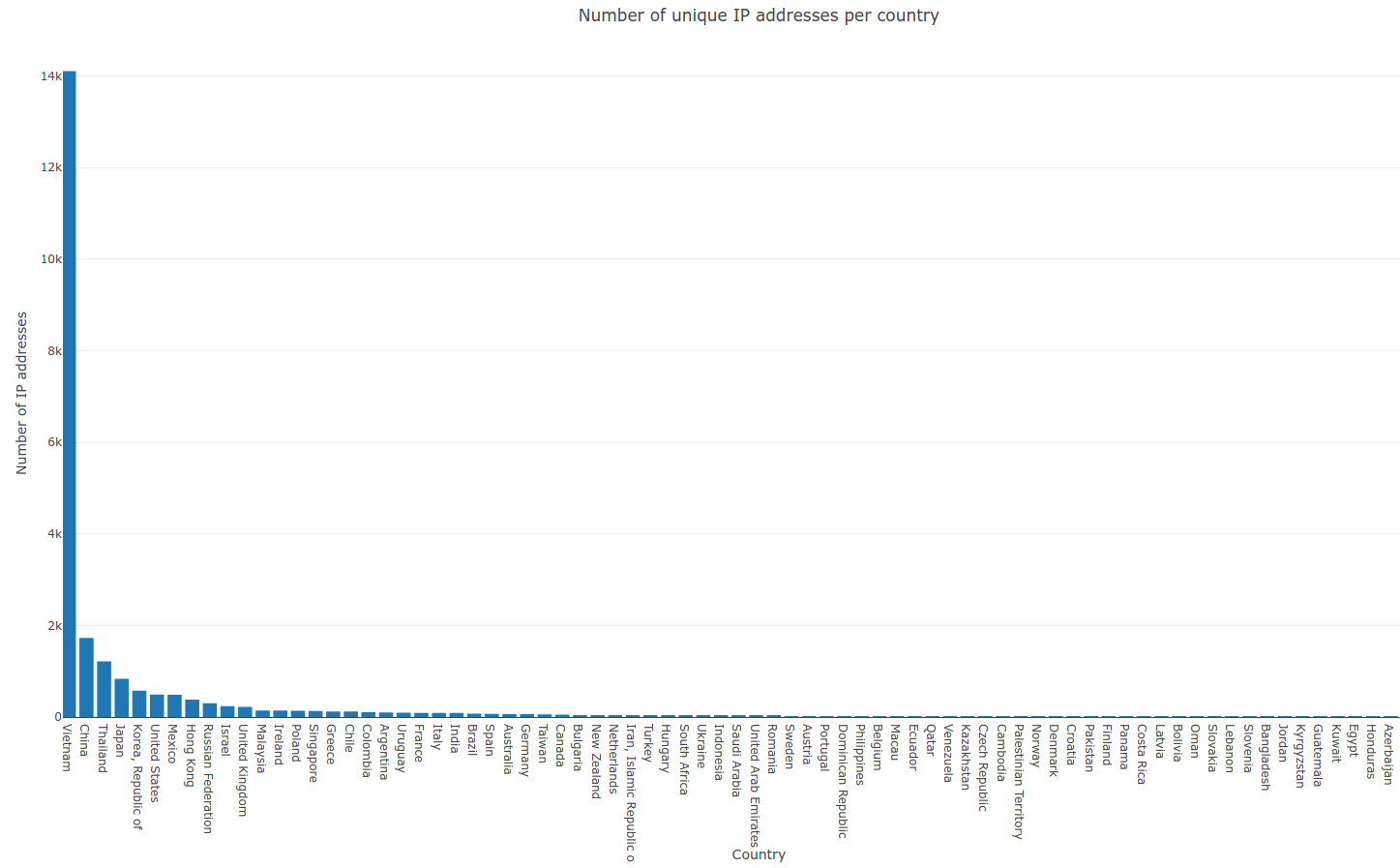
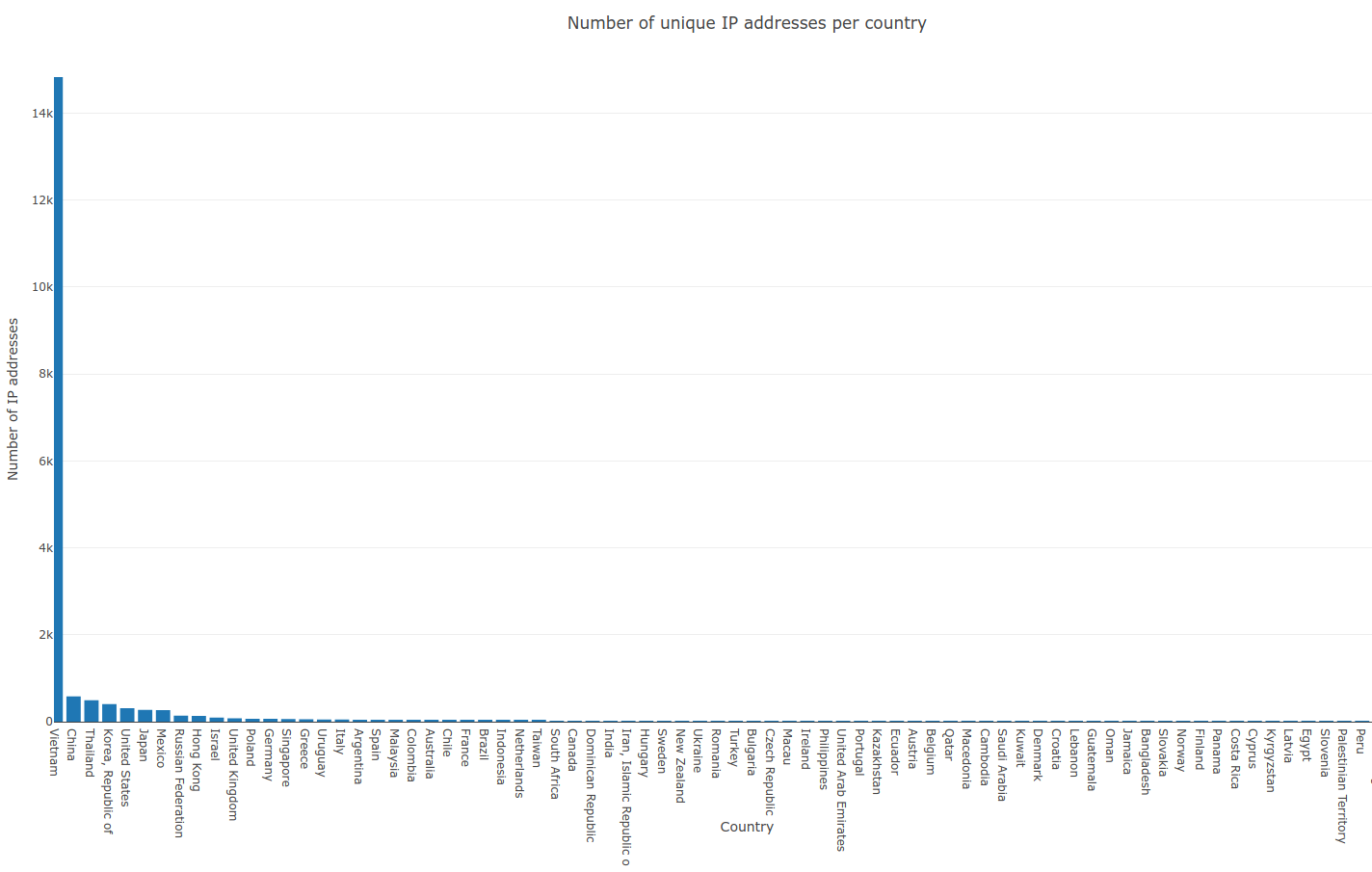
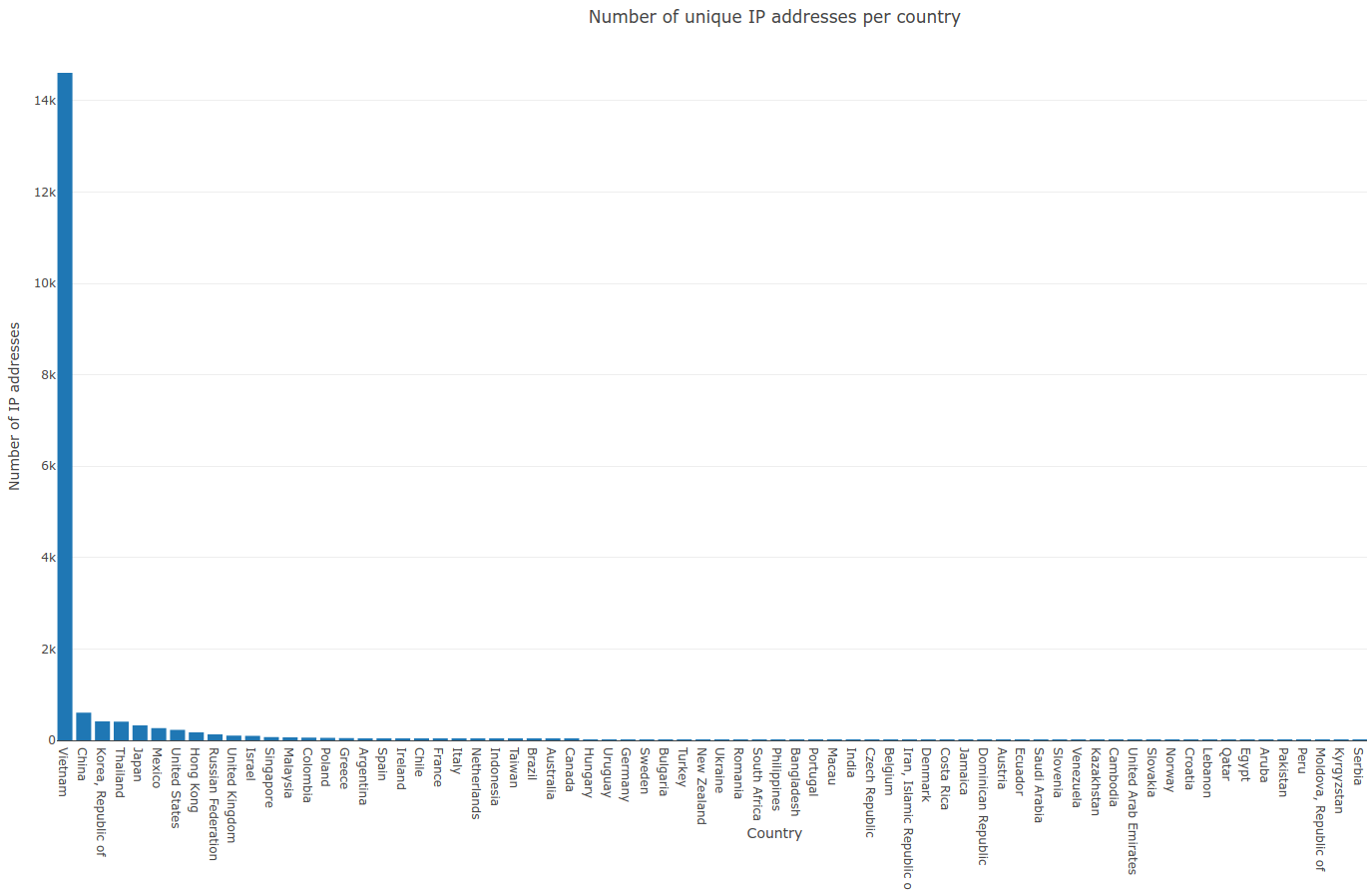
Firstly, let us take a look into the number of total unique source IP addresses. We have noticed 45,393 different IP addresses in total. The biggest number of addresses was noticed in Vietnam, Korea, China, Thailand and Japan.
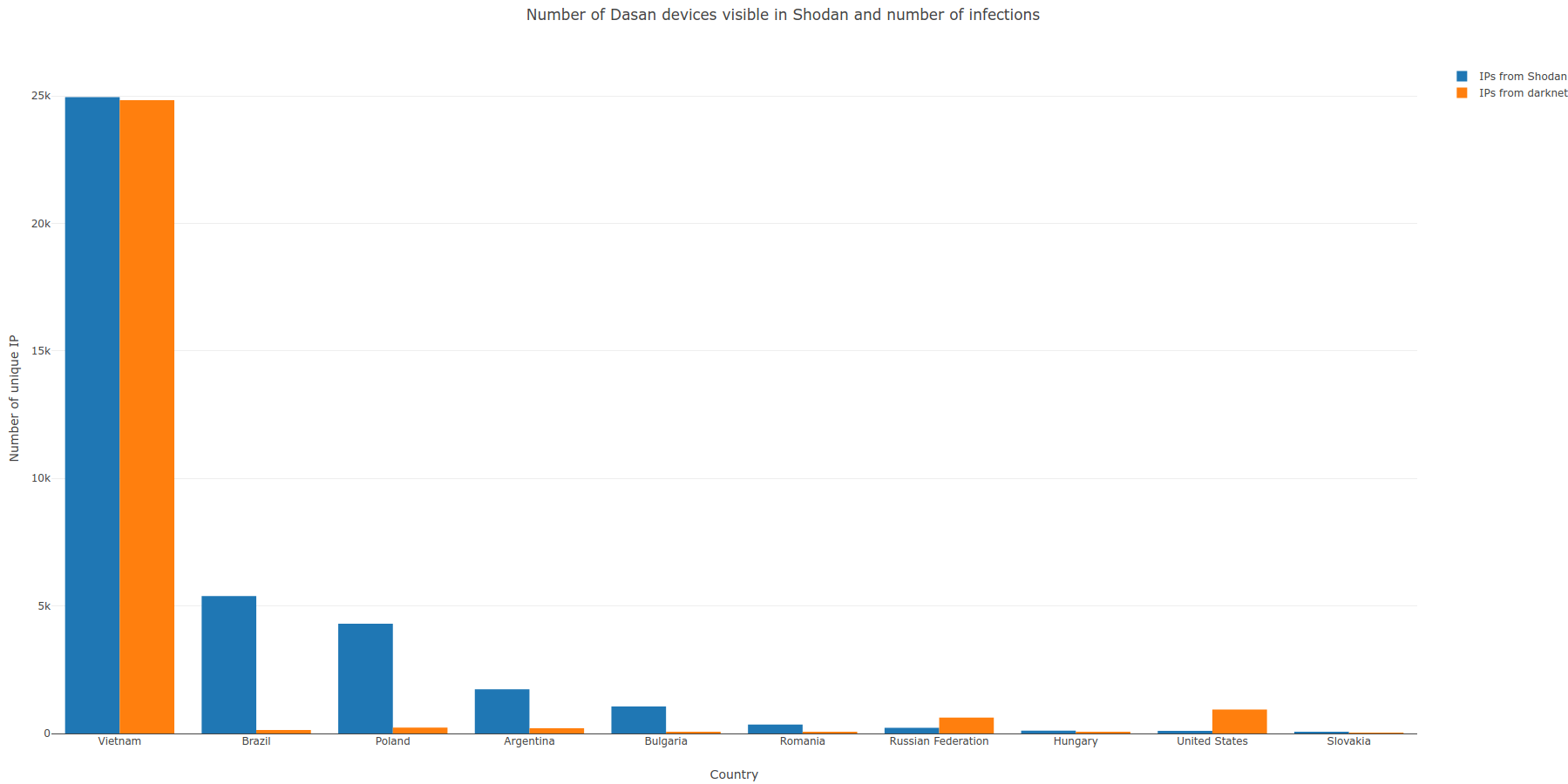
Possible vulnerable devices can be found in Shodan, using the following filter: “DasanNetwork Solution”. However, probably not all of these devices are vulnerable, because there are significant differences between number of devices listed by Shodan and number of devices fingerprinted in darknet. Moreover, number of devices found in Shodan is still getting lower. On 12.02.2018 there were more than 40,000 devices, on 14.02.2018 there were about 38,500 devices and on 15.02.2018 Shodan found only 36,900 devices. Of course we have to remember about DHCP and NAT, so the following chart has an illustrative character only, as it covers almost 4.5 days.
Next chart presents number of packets sent by Satori.Dasan in time (sampled once per 5 minutes). As it can be noticed, the peak was reached around 11.02.2018 00:00 UTC and then the number of scans was gradually decreasing. Major drop down was noticed around 13.02.2018 20:00 UTC.
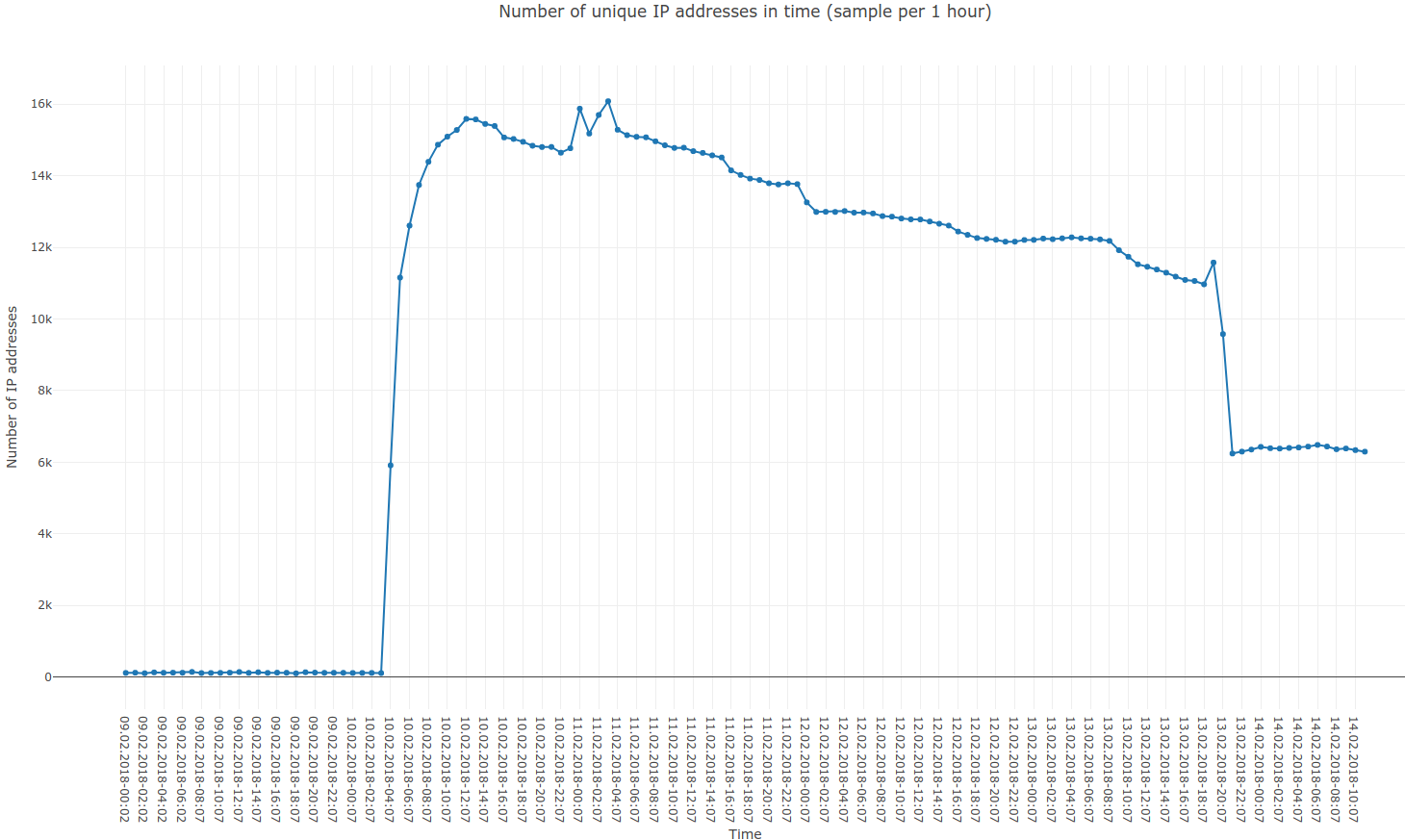
Next charts presents number of unique IP addresses in time (once per 5 minutes and once per 1 hour respectively). During 5 minutes long observations, we have noticed 11,380 unique IP addresses at the peak. On the other hand, during 1 hour observations, we have fingerprinted 16,080 different IP addresses.
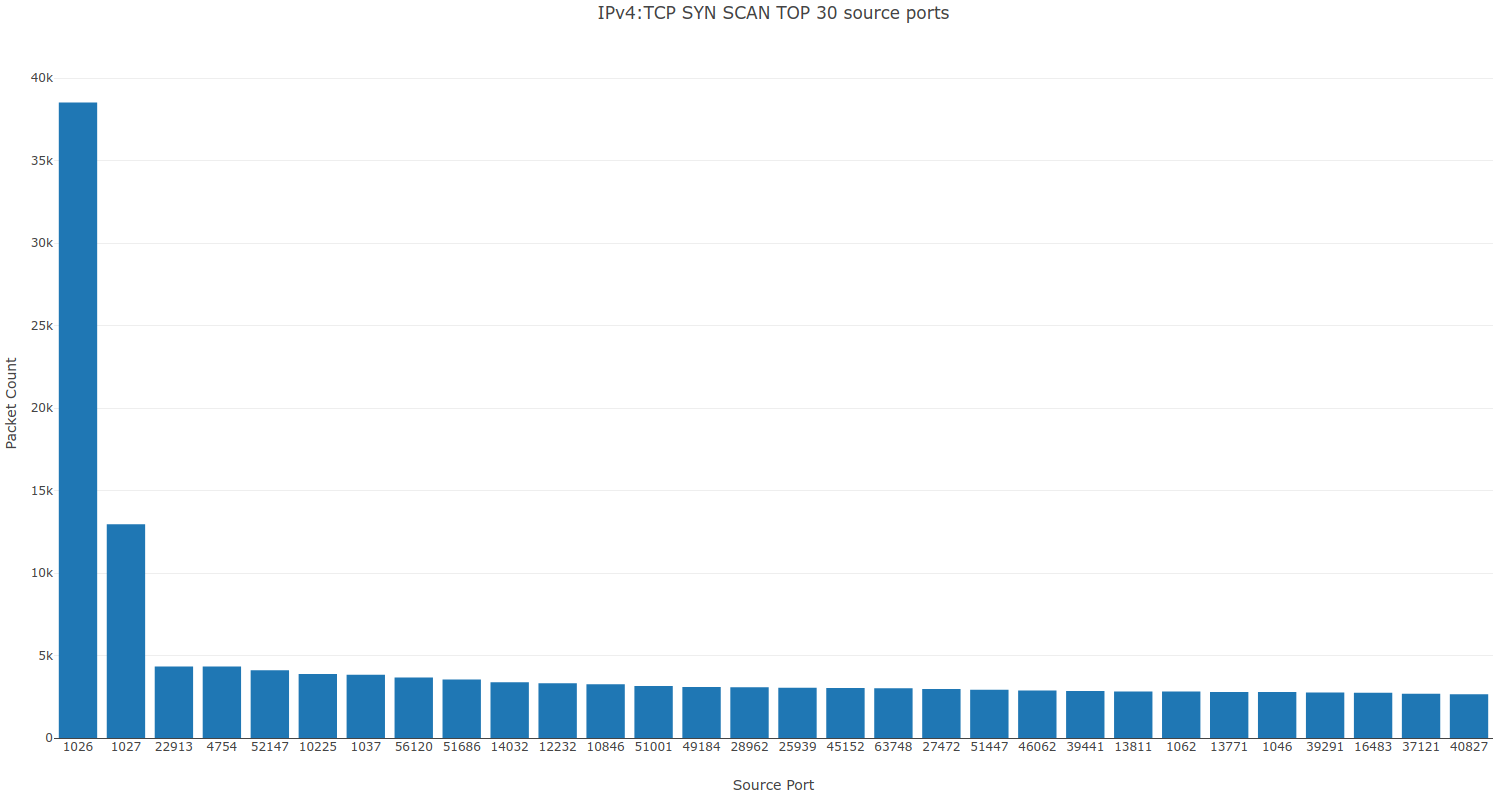
Now, let's have a look at the source ports. Their distribution seems quite normal, despite two suspiciously looking ports: 1026 and 1027. Here is an interesting part: we have fingerprinted about 1,000 unique IP addresses that were using these source ports and almost all of them were located in Vietnam (plus about 10 IP adresses in China).
In the last step, we have checked the daily number of unique IP addresses, for four days when Satori.Dasan was most active.
10.02.2018 - 23,102 unique IP addresses
11.02.2018 - 23,887 unique IP addresses
12.02.2018 - 18,714 unique IP addresses
13.02.2018 - 18,516 unique IP addresses
To sum up, we have fingerprinted about 45,000 unique IP addresses in total, we have observed about 24,000 unique IP addresses on 11.02.2018 and during a period of 1 hour, we have caught a maximum of 16,080 IP addresses. However, some IP addresses were more active during particular periods of time. On this basis, we can safely estimate that Satori.Dasan has infected about 25,000 devices, possibly even 30,000.
In the end, we would like to explain the sudden drop down in the number of scans, which was noticed on 13.02.2018 20:00 UTC. Following chart presents total number of scans observed in darknet on ports 8080, 81 and 52869. It can be easily noticed that the volume of scans on port 52869 and 81 increased at exactly the same time, when the number of scans on port 8080 decreased. According to this, Satori is changing its tactics and is once again targeting Huawei devices and IP cameras.
To sum up, we have estimated that Satori.Dasan variant has infected at least 25,000 devices. The main purpose of Satori is still unknown, thus security community should be on their guard. One thing is sure – people responsible for Satori are still looking for new infection vectors and they probably will not stop in the near future.