The primary data collection mechanism at the heart of the SISSDEN project is a sensor network of honeypots. The sensor network is composed of VPS provider hosted nodes and nodes donated to the project by third-parties acting as endpoints. These VPS nodes/endpoints are not the actual honeypots themselves. Instead, they act as layer 2 tunnels to the SISSDEN datacenter. Attack/scan traffic to the VPS nodes is sent via these tunnels to corresponding VMs which run the actual honeypots themselves. The honeypots in the datacenter then respond to the attacks/scans with the IP addresses from the VPS nodes.
This approach allows for easier management of the honeypots themselves - instead of having to remotely manage (and maintain) honeypots at the VPS provider locations, all can be centrally managed in one datacenter instead.
Each sensor endpoint has multiple IPv4 addresses - one for management, the others for tunneling to the real honeypots. A simplified overview of this technical architecture can be found here.
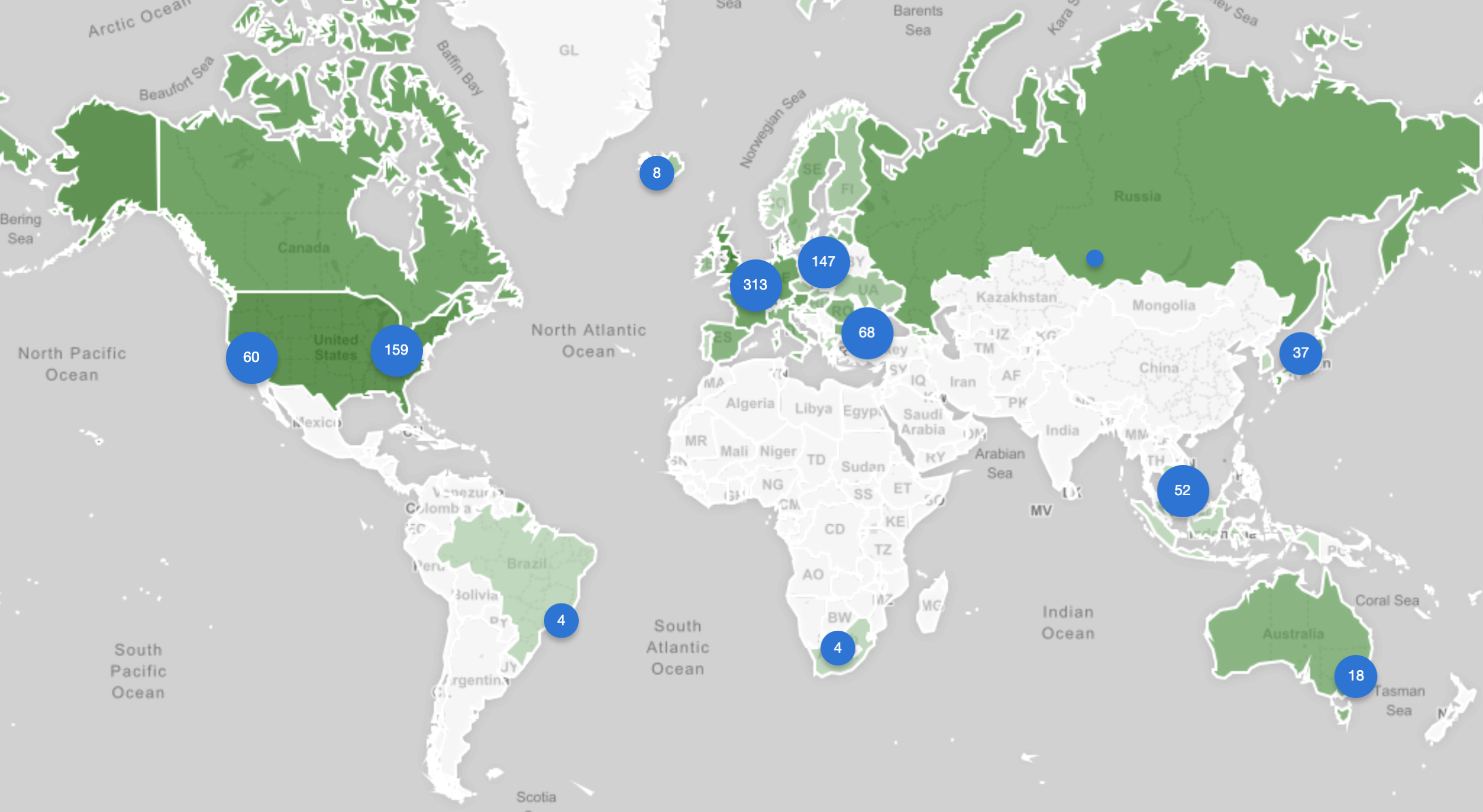
As of 14th of January 2019, SISSDEN has 226 operational nodes running, spread across 58 countries. A total of 953 IP address from 112 ASNs are used, covering 375 /24 networks.
The following world map shows the current snapshat of sensor IPs that are operational:
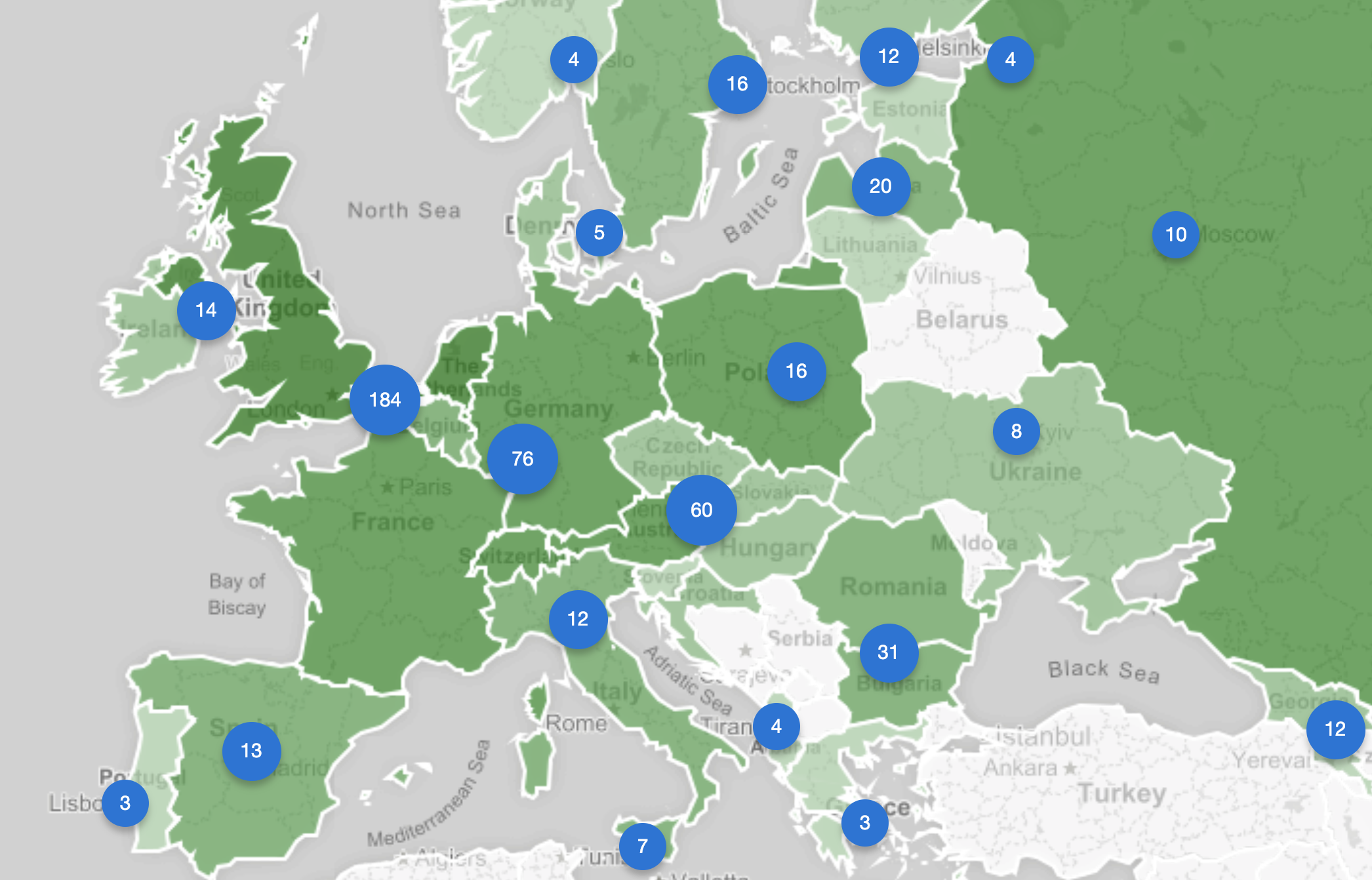
And here is a close up of the IP distribution in Europe:
9 different honeypot types are currently deployed. These are focused on observing different forms of attacks against SSH/telnet services, general or specialised web services, remote management protocols, databases, mail relays, ICS devices etc, including exploits, scans, brute force attempts. Information about these attacks is disseminated to 95+ National CSIRTs and 4200+ network owners via Shadowserver’s free daily remediation feeds. These are marked with source 'SISSDEN'. If you do not receive SISSDEN feeds you can subscribe to them via the SISSDEN Customer Portal.
Contact us if you would like to host of SISSDEN sensor. Requirements are low.
Each sensor is a VM with at least:
- 1 core
- 512MB RAM (1GB recommended)
- 5 GB hard drive (10GB recommended)
- 2 or more static IPv4 addresses (4 would be optimal, on a single NIC, no NAT, unfiltered)
The VM must be running Ubuntu 16.04 LTS. The virtualization technology should be either KVM, Xen or VMWare. We expect root access (SSH) and full control over the VM. Our configuration management will manage the VM. As described these machines will only be used as tunnel endpoints (layer 2 tunneling) to our datacenter and honeypots in the datacenter will respond to the requests to these endpoints. Please consider making a sensor donation and help us make the Internet a more secure environment by contacting us through the SISSDEN Customer Portal.